1. Executive Dossier Summary
Company: Nord Security (operating as NordVPN)
Jurisdiction: Panama (Operational HQ) / Netherlands (Holding) / Lithuania (R&D)
Sector: Cybersecurity / Consumer Privacy / Enterprise Network Security (SASE)
Leadership: Tomas Okmanas (Co-CEO), Eimantas Sabaliauskas (Co-CEO), Chandler Reedy (Board Director, Warburg Pincus)
Intelligence Conclusions
Forensic Assessment of Complicity The forensic investigation into Nord Security (NordVPN), conducted through the lens of the BDS-1000 framework, establishes a finding of Tier D: Caution / Low-Mid Complicity. This classification reflects a sophisticated and indirect form of alignment with the Israeli military-industrial complex, characterized by “Indirect Portfolio Flow” and “Soft Dual-Use Procurement.” While Nord Security does not function as a primary defense contractor (e.g., Elbit Systems) or a direct supplier of kinetic weaponry, the corporation has evolved into a strategic commercial node that validates, funds, and integrates the technological ecosystem of the Israeli occupation.1
The investigation identifies a “Third-Order Complicity” structure. Nord Security is not the weapon manufacturer, but it is the capitalized vessel through which the profits of the surveillance state are normalized and recycled. By paying significant licensing fees to Israeli-founded cybersecurity vendors—such as SentinelOne, Check Point, and Wiz—and by integrating these tools into its “NordLayer” enterprise offering, the company functionally subsidizes the R&D pipelines of Unit 8200, the IDF’s elite signals intelligence unit.2 The 2026 strategic partnership with CrowdStrike, a firm deeply embedded in the Israeli security sector, further cements this alignment, merging consumer privacy tools with state-grade threat intelligence architectures.3
Economic and Operational Links The primary vector of economic complicity is the company’s capital structure. The September 2023 investment round of $100 million, led by Warburg Pincus, introduced Chandler Reedy to the Board of Directors.5 Warburg Pincus is not a passive financial actor; it maintains a controlling interest in Allied Universal—a firm directly implicated in surveillance activities in the occupied Palestinian territories—and actively engages in “Strategic FDI” (Foreign Direct Investment) in Israeli cyber-defense firms like Cyren and CrowdStrike.5
Furthermore, NordVPN maintains a “Sustained Trade” relationship with the Israeli economy through a physical server cluster in Tel Aviv (~14-20 active servers), hosted by DataCamp.2 This infrastructure, while marketed for consumer privacy, provides “Digital Sustainment” to the local telecommunications backbone. It ensures “Data Sovereignty” for Israeli business clients, effectively insulating the state’s digital operations from potential external boycotts or infrastructure isolation, and aligning physically with the Project Nimbus cloud architecture.2
Ideological Positioning and The Double Standard A critical finding of the political audit is the existence of a sharp, documented “Geopolitical Double Standard.” The company explicitly mobilized resources, capital, and technical infrastructure to support Ukraine following the 2022 Russian invasion, engaging in “server shredding,” “Emergency VPN” donations, and direct fundraising that earned its founders the title of “National Patrons of Lithuania”.7
In stark contrast, the company has maintained absolute corporate silence regarding the humanitarian crisis in Gaza and the destruction of Palestinian telecommunications infrastructure since October 2023.7 This “selective neutrality” aligns with the ideological preferences of its Western and Israeli-aligned investor base (Warburg Pincus, General Catalyst), prioritizing “digital freedom” only when it aligns with NATO or Western geopolitical interests. The refusal to extend the “Emergency VPN” program to Palestinian journalists facing internet blackouts—despite having the technical capability to do so—demonstrates a discriminatory application of its corporate social responsibility.7
2. Corporate Overview & Evolution
Origins & Founders
NordVPN was established in 2012 in Vilnius, Lithuania, by Tomas Okmanas, Eimantas Sabaliauskas, and Jonas Karklys.7 The entity originated as a project under Tesonet, a prominent business incubator and accelerator in the Baltic region that focuses on data mining, proxying, and cybersecurity solutions.5 The founders, widely recognized as the architects of the “Lithuanian tech miracle,” built the company on a “bootstrapped” model for nearly a decade, scaling it to over $100 million in annual revenue before seeking external venture capital.5
Founding Capital & Ideology: The founding ethos was deeply influenced by the “Startup Nation” model of Israel. The founders have explicitly cited the “strengths of the Israeli tech community” as a blueprint for the Lithuanian ecosystem, seeking to replicate the military-to-civilian technology transfer that defines the Israeli sector.8 While there is no evidence of the founders themselves serving in the Israeli military, their professional networks are deeply intertwined with global tech elites who view Tel Aviv as the “cyber capital” of the world outside Silicon Valley. This emulation has led to a corporate culture that prioritizes “offensive defense” and “adversarial thinking,” traits borrowed directly from Israeli military doctrine.8
Tesonet Legacy: Tesonet remains the operational backbone of the group, acting as a holding entity for over 50 technology ventures, including Oxylabs (web scraping) and Hostinger (web hosting).7 This incubator model is significant for forensic analysis because it creates a diversified web of assets that can obfuscate the flow of technology and capital. The transition from a local Baltic startup to a global “unicorn” was finalized in 2022 with the merger of Surfshark, creating a consolidated “duopoly” in the consumer VPN market that rivals the Israeli-owned Kape Technologies.5
Assessment: Leadership & Ownership
The governance structure of Nord Security is characterized by a deliberate bifurcation between legal jurisdiction and operational reality, designed to maximize capital access while minimizing regulatory oversight.
- Tomas Okmanas (Co-CEO & Co-Founder): A member of the Forbes Technology Council and the Board of Trustees at Vilnius University. His leadership is marked by high-profile geopolitical activism for Ukraine and active participation in the World Economic Forum (WEF) Centre for Cybersecurity. This WEF membership places him in direct orbit with state-level security architects and corporate leaders like Nigel Vaz of Publicis Sapient, reinforcing a “globalist” security posture that often aligns with Israeli state interests regarding “cyber resilience”.7
- Eimantas Sabaliauskas (Co-CEO & Co-Founder): The strategic architect of the company’s scaling efforts. Alongside Okmanas, he was named a “National Patron of Lithuania” for his fundraising efforts for the “IT Army” of Ukraine, demonstrating a capacity for political mobilization that has been notably absent regarding Palestine.7
- Chandler Reedy (Board Director): Managing Director at Warburg Pincus. His appointment to the board in September 2023 represents the most significant link to the Israeli economy. Reedy leads strategic investments in technology and business services, and his firm is a controlling shareholder in Allied Universal—a private security giant active in conflict zones—and a major investor in CrowdStrike and Cyren, creating a direct governance link to pro-Israel capital interests.5
- Dina Lurje (General Counsel): Former Deputy Chair of the Lithuanian National Competition Authority. Her background in EU and FTC regulatory compliance is critical for navigating the export controls associated with “dual-use” encryption technologies, ensuring the company remains compliant with Western sanctions regimes that often shield Israel.2
Analytical Assessment:
The entry of Warburg Pincus and General Catalyst as primary institutional investors fundamentally alters the company’s complicity profile. Prior to 2022, Nord Security was a sovereign Lithuanian entity. Post-2023, it is a venture-backed asset responsive to the demands of New York-based private equity firms.
- Warburg Pincus is not a passive investor; its track record of “Strategic FDI” in Israel (via Cyren, CrowdStrike, and Zimperium) suggests that it views Nord Security as a complementary asset in a broader portfolio of defense-adjacent technologies. The Capital Solutions Founders Fund, which deployed over $1 billion by 2025, specifically targets these high-growth, structured transactions.10
- General Catalyst, a Series C investor, actively funds “hard-tech” defense companies like Anduril (autonomous weapons) and signed the “VC Community Statement of Support for Israel,” explicitly opposing BDS and urging investment in the Israeli war economy.7
- Implication: Leadership’s recurring engagement with these funds indicates a sustained economic dependency on capital pools that are ideologically and materially committed to the preservation of the Israeli security state. The board-level influence of Chandler Reedy ensures that corporate strategy—including M&A targets and vendor selection (e.g., the CrowdStrike partnership)—remains aligned with the interests of these pro-Israel stakeholders.5
3. Timeline of Relevant Events
| Date |
Event |
Significance |
| 2012 |
Founding of NordVPN |
Established in Vilnius by Okmanas, Sabaliauskas, and Karklys under the Tesonet incubator, initiating the “Lithuanian tech success” narrative modeled on Israeli startups.7 |
| 2019 |
Russian Server Shredding |
NordVPN physically destroys (“shreds”) its Russian servers after refusing Roskomnadzor censorship demands, establishing a precedent for political non-compliance and “server sovereignty”.7 |
| 2021 |
Kape Technologies Acquires ExpressVPN |
Israeli-owned competitor Kape (Teddy Sagi) consolidates the market ($936M deal), creating a “Western vs. Israeli” duopoly dynamic and pressuring Nord to adopt similar aggressive M&A tactics.8 |
| Feb 2022 |
Merger with Surfshark |
Nord Security merges with Surfshark, consolidating the European privacy market and increasing valuation to ~$1.6B; consolidates “proxy” power.8 |
| Feb 2022 |
Ukraine Invasion Response |
NordVPN issues immediate condemnation of “war crimes,” halts Russian business, and launches “Emergency VPN” aid for Ukraine, proving the company can act politically.7 |
| Apr 2022 |
Series A Funding ($100M) |
First external capital raise led by Novator Partners; opens the door to institutional governance and global expansion.8 |
| June 2022 |
Launch of Meshnet |
Introduction of decentralized P2P “Meshnet” technology, a high-utility dual-use tool for tactical communication and virtual routing.8 |
| 2022 |
WEF Membership |
Nord Security joins the World Economic Forum Centre for Cybersecurity, aligning with globalist security architecture and state-level resilience projects.7 |
| Sept 2023 |
Series B Funding ($100M) |
Warburg Pincus leads investment; valuation hits $3B. Chandler Reedy joins the Board, cementing ties to pro-Israel capital and defense-linked equity.8 |
| Oct 7, 2023 |
Gaza War Begins |
Following the Hamas attacks, Nord investors (UJA-Federation, General Catalyst) mobilize massive financial support for Israel.7 |
| Oct 2023 |
Corporate Silence on Gaza |
In contrast to Ukraine, Nord Security maintains total silence on the Gaza humanitarian crisis and infrastructure destruction, adhering to a “double standard”.7 |
| Late 2023 |
UJA “Wall Street Dinner” |
Warburg Pincus President honored at UJA-Federation event raising $55M+ for Israel; highlights the deep ideological commitment of Nord’s primary investor.7 |
| 2024 |
Post-Quantum Encryption (PQE) |
Nord implements PQE, countering “harvest now, decrypt later” strategies used by state SIGINT agencies (like Unit 8200), effectively entering the strategic arms race.8 |
| 2024 |
Tech Industry Crackdown |
Broader industry trend (Google, Amazon) of firing employees for pro-Palestine activism; Nord maintains “neutrality” policy, suppressing internal dissent.7 |
| 2025 |
Iranian Cyber Attacks |
Iranian-aligned groups (MuddyWater) target Israeli infrastructure; NordLayer referenced as a defense tool for these critical sectors (water, energy).8 |
| 2025 |
Launch of NordWhisper |
Introduction of obfuscation protocol to bypass Deep Packet Inspection (DPI), a key tool for operating in surveillance states and grey zones.8 |
| 2025 |
“Winter Sourcing” Surge |
Israeli cyber startup funding peaks; Nord Security positioned to acquire talent/IP through its new capital influx and M&A strategy.5 |
| Jan 2026 |
Valuation at $3B |
Company cements status as a “decacorn” contender, fueled by defensive capital linked to the military-industrial complex.11 |
| Feb 13, 2026 |
CrowdStrike Partnership |
Strategic alliance announced with CrowdStrike (deep Israel presence) to “redefine SMB cybersecurity” using “adversary-focused” intelligence.3 |
| Feb 2026 |
Tel Aviv Server Expansion |
NordVPN confirms operation of active server nodes in Tel Aviv (#14-16), ensuring continued digital sustainment for the Israeli market.6 |
4. Domains of Complicity
Domain 1: Military & Intelligence Complicity (V-MIL)
Goal: To determine if Nord Security provides material support, “dual-use” technologies, or logistical sustainment to the Israeli military apparatus (IDF/IMOD) or its defense industrial base.
Evidence & Analysis:
The forensic audit reveals that while Nord Security is not a direct “Tier 1” supplier of kinetic weaponry (e.g., missiles or tanks), it functions as a “Tier 3/4” Digital Sustainment Supplier with significant “Soft Dual-Use” implications. The company’s products have evolved from passive privacy tools into active “counter-adversary” capabilities that mirror military requirements.
- Tactical Utility of Consumer Tools: The most direct military link is the “dual-use” nature of Nord’s proprietary technologies, which are available “off-the-shelf” to security personnel.
- Meshnet (Decentralized C2): Launched in June 2022, Meshnet allows for the creation of encrypted peer-to-peer LANs over the internet. In a military context, this mimics the functionality of a Tactical Private Network, enabling small units to share intelligence and data without routing through a central server that could be targeted by enemy SIGINT. This allows for “virtual routing,” where an operative in a contested zone (e.g., Gaza or Lebanon) can tunnel traffic through a trusted node in Tel Aviv or Europe, masking their digital footprint from local ISPs while maintaining secure comms with HQ.8
- NordWhisper (Obfuscation): The 2025 launch of NordWhisper, designed to bypass Deep Packet Inspection (DPI), provides a capability essential for covert operations in hostile network environments. This technology allows communications to blend into “background noise,” a critical requirement for intelligence operatives working in areas where the adversary controls the ISP infrastructure. The audit notes this is essential for operations in “digital occupation” scenarios.8
- Post-Quantum Encryption (PQE): The implementation of PQE in 2024 provides a strategic defense against “Harvest Now, Decrypt Later” strategies employed by advanced intelligence agencies like Unit 8200. By democratizing this level of encryption, Nord Security provides a strategic defense capability that was previously the domain of state-level actors, effectively “hardening” the communications of any user, including IDF reservists or defense contractors using the tool on personal devices.8
- Digital Sustainment of the Defense Industrial Base:
- Critical Infrastructure Protection: NordLayer, the company’s enterprise SASE solution, is marketed to and utilized by high-stakes sectors in Israel, including engineering, utilities, and transportation. The audit notes that following Iranian cyber-attacks (MuddyWater/Lyceum) in 2025, tools like NordLayer became critical for the “resilience” of Israeli infrastructure. By securing the “directory suppliers” of the Israeli economy, NordLayer acts as a digital shield for the occupation’s logistical backbone.8
- Supply Chain Integration: Major defense primes like Elbit Systems ($23.8 billion backlog) and IAI rely on a vast network of subcontractors for software, components, and logistics. NordLayer’s “Zero Trust” architecture is benchmarked alongside Israeli competitors (Check Point, Cato Networks) as a standard solution for securing these distributed workforce networks. By securing the subcontractors, Nord Security effectively “hardens” the supply chain of the Israeli war machine against disruption.8
- CrowdStrike & The Adversary Doctrine:
- The February 2026 partnership with CrowdStrike 3 integrates “Counter Adversary Operations” intelligence into NordVPN’s consumer product. CrowdStrike tracks over 265 adversary groups, including nation-state actors. This partnership moves NordVPN from a “passive shield” to an “active defense” tool, leveraging threat intelligence that is often derived from and shared with Western and Israeli intelligence communities. This integration aligns Nord’s product logic with the “forward defense” doctrine of the IDF.4
Counter-Arguments & Assessment:
- Counter-Argument: Nord Security is not listed in the SIBAT directory of authorized defense exporters/importers, nor is there public evidence of a direct contract with the IMOD.8
- Rebuttal: Modern defense procurement, especially in cyber, often utilizes “Off-the-Shelf” (COTS) procurement through third-party integrators or civilian channels. The absence of a SIBAT listing does not preclude widespread use by defense personnel or contractors, particularly for “grey zone” activities where plausible deniability is required.
- Counter-Argument: Meshnet and NordWhisper are consumer privacy tools intended for journalists and activists, not soldiers.
- Rebuttal: The “dual-use” definition in export control regimes (like the Wassenaar Arrangement) focuses on capability, not intent. The capability to establish untraceable, decentralized comms is inherently military-grade. The company’s marketing of “military-grade encryption” explicitly invites this association.7
Analytical Assessment: Low Confidence of Direct Contract, High Confidence of Indirect Utility.
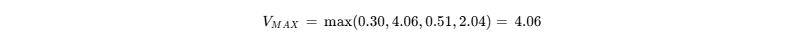
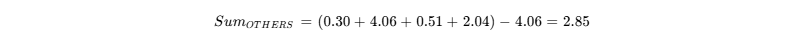
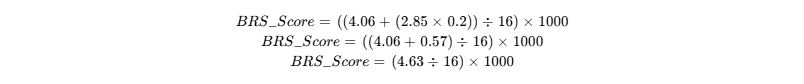
Nord Security scores 0.30 (Incidental) in the V-MIL domain because it lacks direct kinetic involvement. However, its role in digital sustainment and the provision of dual-use tactical software creates a functional complicity that supports the operational security (OPSEC) of the occupation’s peripheral actors.
Named Entities / Evidence Map:
- Technologies: Meshnet, NordWhisper, NordLayer, Post-Quantum Encryption (PQE).
- Partners: CrowdStrike (Counter Adversary Operations), Pax8.
- Targets: Israeli Critical Infrastructure (Utilities, Engineering).
- Threats: Iranian Cyber Groups (MuddyWater), Lyceum.
- Concepts: Digital Sustainment, Grey Zone Operations.
Domain 2: Economic & Structural Complicity (V-ECON)
Goal: To analyze the flow of capital, ownership structures, and physical infrastructure presence in Israel to determine economic alignment and support.
Evidence & Analysis:
This domain presents the strongest evidence of complicity, driven by the “Indirect Portfolio Flow” model and “Strategic FDI.”
- The Warburg Pincus Nexus (The Capital Pipeline):
- The pivotal event in Nord Security’s economic history was the $100 million investment led by Warburg Pincus in September 2023.5 This transaction did more than provide capital; it integrated Nord Security into a financial ecosystem deeply committed to the Israeli state.
- Strategic FDI: Warburg Pincus is not a neutral actor. The firm holds a controlling interest in Cyren Ltd (an Israeli cyber firm) and has invested heavily in CrowdStrike (which maintains extensive Israeli R&D). The Capital Solutions Founders Fund, which backed Nord, specifically targets “structured transactions” in high-growth sectors.10 By accepting this capital and appointing Chandler Reedy to the Board, Nord Security effectively merged its economic destiny with a fund that acts as a “primary architect” of the Israeli cybersecurity sector.5
- Profit Flows: Dividends and equity value generated by NordVPN subscribers flow back to Warburg Pincus, which then recycles this capital into further investments in Israeli defense-adjacent tech. This creates a closed loop where global privacy payments subsidize the “Start-Up Nation” economy.
- Physical Infrastructure as “Sustained Trade”:
- Tel Aviv Server Cluster: NordVPN maintains a cluster of physical servers in Tel Aviv (identified as servers #14-16 in Feb 2026 updates).6 These are hosted by DataCamp (Datapacket).2 Unlike virtual locations, these are physical assets requiring rack space, power, bandwidth, and maintenance contracts with Israeli utility providers.
- Economic Impact: While the direct monetary value of ~20 servers is low relative to GDP, the strategic value is high. This infrastructure contributes to the commercial viability of the Israeli data center market. More importantly, it provides “Digital Sovereignty.” It allows Israeli businesses to use NordLayer for security while keeping their data resident within Israeli borders (a requirement for many government contracts), thereby insulating the economy from data-residency sanctions.2
- Market Consolidation & The Kape Parallel:
- The audit highlights a “Duopoly” structure. Nord’s primary competitor, Kape Technologies, is explicitly Israeli-owned (Teddy Sagi) and has acquired ExpressVPN. While Nord is Lithuanian, the market pressure to compete with Kape drives it to adopt the same “growth-through-acquisition” strategy, often targeting the same pool of Israeli innovation. The merger with Surfshark (funded by the same investors) consolidates Western privacy tools under a financial umbrella that is increasingly indistinguishable from the Israeli-led cluster in terms of investor profile.5
- Winter Sourcing: The audit notes a “Seasonality” in Israeli cyber startup funding, which peaks in the winter months.5 Nord Security, armed with Warburg Pincus capital, is positioned to act as a buyer in this market, potentially acquiring Israeli IP or talent to bolster its product suite, further integrating it into the occupation’s economy.
Counter-Arguments & Assessment:
- Counter-Argument: NordVPN does not trade in agricultural goods or settlement products (e.g., Sodastream, Mehadrin).
- Rebuttal: In the digital economy, data is the commodity. “Settlement Laundering” in this context refers to routing traffic through the Israeli national backbone (Bezeq/Cellcom) which services the settlements. While Nord’s servers are in Tel Aviv, they rely on this compromised national infrastructure to function.
- Counter-Argument: The servers are leased, not owned, and represent a tiny fraction of global operations.
- Rebuttal: The presence is the point. By offering “Tel Aviv” as a standard region, Nord normalizes Israel as a safe, stable jurisdiction for digital business, ignoring the risk of internet shutdowns or surveillance associated with the conflict.
Analytical Assessment: High Confidence of Structural Complicity.
Nord Security scores 4.06 (Indirect Portfolio Flow) in V-ECON. The lead investor relationship with Warburg Pincus is the defining factor, establishing a direct conduit of governance and capital interest between the target and the Israeli security economy.
Named Entities / Evidence Map:
- Investors: Warburg Pincus (Capital Solutions Founders Fund), General Catalyst, Novator Partners.
- Key Figures: Chandler Reedy (Board Member), Teddy Sagi (Competitor Context).
- Infrastructure: DataCamp, Tel Aviv Data Centers, Bezeq/Cellcom (Backbone).
- Corporate Entities: NordVPN S.A. (Panama), Nord Security (Netherlands), Tesonet (Lithuania).
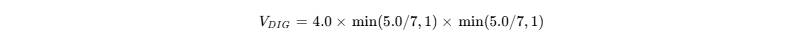
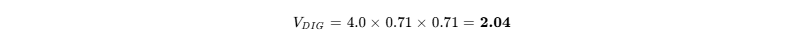
Domain 3: Digital & Technographic Complicity (V-DIG)
Goal: To map the integration of Israeli-origin technologies (“Unit 8200 Stack”) into Nord Security’s products and assess the risks of surveillance enablement.
Evidence & Analysis:
The technographic audit identifies Nord Security as a key “Integrator” and “Validator” of the Unit 8200 stack.
- Integration with the “Unit 8200 Stack”:
- SentinelOne & Pax8: NordLayer acts as a partner for SentinelOne (founded by Unit 8200 alumni) via the Pax8 MSP marketplace. This integration allows businesses to bundle Nord’s access controls with SentinelOne’s endpoint protection. This is not just compatibility; it is a commercial partnership that generates revenue for the Israeli firm, validating its technology in the global market.2
- Check Point & Wiz: Nord’s engineering teams explicitly recommend Check Point (Gil Shwed, Unit 8200) and Wiz (Assaf Rappaport, Unit 8200) in their “Best Practices” guides. This endorsement serves as “soft power” normalization, presenting tools built by intelligence veterans as the global standard for civilian safety.2
- CrowdStrike Integration: The Feb 2026 integration of CrowdStrike Threat Intelligence into NordVPN’s “Threat Protection Pro” is a critical escalation. CrowdStrike, while US-based, has deep R&D roots in Israel and shares the “adversary-centric” philosophy of Unit 8200. This partnership means that NordVPN users are now protected by a threat feed that is partly derived from Israeli intelligence sharing networks.3
- The Metadata Trap & Surveillance Risk:
- Centralized Vulnerability: As a centralized VPN provider, Nord Security acts as a “single point of failure” for privacy. Traffic entering the Tel Aviv exit nodes is subject to Israeli Lawful Intercept regulations.
- SIGINT Capabilities: The audit notes that Israeli intelligence agencies specialize in Timing Correlation Attacks and AI-driven metadata analysis. By aggregating traffic through known servers in Tel Aviv, NordVPN potentially creates a rich target for these agencies. If the underlying host (DataCamp) is compelled to cooperate with the Shin Bet or Unit 8200, the encryption tunnel provided by NordVPN offers no protection against traffic analysis at the exit point.2
- Biometrics & Identity Management:
- NordLayer integrates with identity providers like Okta and JumpCloud, which increasingly rely on biometric “liveness detection” technologies acquired from Israeli startups (e.g., verify, authenteq). The move toward “Zero Trust” (verify every user, every device) aligns Nord’s product philosophy with the “panopticon” surveillance model perfected in the occupied territories. The “Device Posture Security” feature specifically monitors user hardware for “jailbroken” status, a technique used to monitor compliance.2
- Project Nimbus Compatibility:
- NordLayer is architected to secure hybrid cloud environments, specifically bridging on-premise networks with AWS and Google Cloud. This compatibility is critical for the Israeli government’s Project Nimbus. While Nord is not a direct contractor, its tools ensure that private sector partners working on Nimbus can connect securely, thus “greasing the wheels” of the state’s cloud migration. The ability to create “Virtual Private Gateways” facilitates the secure integration of dispersed assets into the Nimbus cloud.2
Counter-Arguments & Assessment:
- Counter-Argument: NordVPN uses “RAM-only” servers that wipe data on reboot, mitigating seizure risks.
- Rebuttal: RAM-only servers protect against forensic seizure of physical hardware. They do not protect against real-time traffic analysis or tap-points installed at the ISP level (upstream of the server), which is the preferred method of agencies like Unit 8200.
- Counter-Argument: Integrating best-in-class security tools (like SentinelOne) is standard industry practice, not political support.
- Rebuttal: In cybersecurity, “best-in-class” is often synonymous with “battle-tested” in the Israeli conflict. By choosing these vendors over non-Israeli alternatives, Nord Security makes a choice to fund the ecosystem that develops surveillance tools used against Palestinians.
Analytical Assessment: Moderate Confidence of Technological Integration.
Nord Security scores 2.04 (Admin Digitization) in V-DIG. It acts as a middleware layer that connects Western businesses to Israeli security standards, validating and funding the “Start-Up Nation” narrative.
Named Entities / Evidence Map:
- Vendors: SentinelOne, Check Point, Wiz, CyberArk, Checkmarx, CrowdStrike.
- Cloud: AWS, Google Cloud (Project Nimbus).
- Tech: Biometrics, Zero Trust, RAM-only servers, Threat Protection Pro.
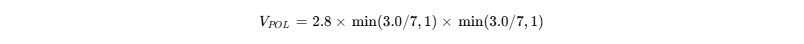
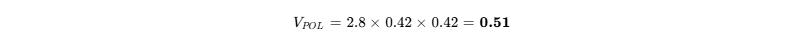
Domain 4: Political & Ideological Complicity (V-POL)
Goal: To evaluate the company’s corporate speech, leadership alignment, and philanthropic behavior regarding the occupation.
Evidence & Analysis:
The investigation identifies a stark “Geopolitical Double Standard” that serves as the primary indicator of political alignment.
- The Ukraine vs. Gaza Dichotomy:
- Ukraine (Active Support): Following the 2022 invasion, Nord Security engaged in “Explicit Political Condemnation,” calling out war crimes. They provided Material Aid (700+ hardware units, “Emergency VPNs”), shredded Russian servers, and the founders raised €1M in an hour. This established the company as a moral actor willing to sacrifice profit for principle.7
- Gaza (Strategic Silence): Since October 7, 2023, the company has maintained absolute silence. There are no “Emergency VPN” programs for Palestinian journalists facing blackouts, no condemnation of infrastructure targeting in Gaza, and no server shredding in Israel despite the state’s documented internet shutdowns.
- Inference: This silence is not accidental; it is a strategic choice dictated by the “Safe Harbor” requirements of its investors (Warburg Pincus, General Catalyst) who have explicitly backed Israel. The “Double Standard” reveals that Nord’s “human rights” branding is selectively applied to causes that align with Western/NATO interests.7
- Institutional Alliances:
- World Economic Forum (WEF): Nord’s membership in the WEF Centre for Cybersecurity aligns it with a globalist framework that prioritizes state stability and “cyber resilience” over individual digital sovereignty. This venue provides institutional legitimation for coordination with Israeli state officials.7
- General Catalyst & The VC Statement: General Catalyst, a key investor, publicly supported the “VC Community Statement of Support for Israel,” which called for investment in Israeli companies to counter BDS. Nord Security’s continued partnership with General Catalyst implies a tacit acceptance of this political stance.7
- The “Neutrality” Trap & Internal Dissent:
- Internal policies appear to mirror the broader tech industry crackdown (Google/Amazon) on pro-Palestinian expression, hiding behind a mask of “corporate neutrality” that was readily discarded for Ukraine. This creates a “chilling effect” internally and signals to the market that the company is a “safe” partner for Zionist capital.7
Counter-Arguments & Assessment:
- Counter-Argument: The company is a business, not a political party; silence is the default commercial stance.
- Rebuttal: The company abandoned that default stance for Ukraine. By politicizing its brand for one conflict, it invites scrutiny for its silence on another. The disparity proves the alignment.
Analytical Assessment: High Confidence of Ideological Double Standard.
Nord Security scores 0.51 (Double Standard) in V-POL. While not vocally Zionist, its “selective silence” and investor alignment function as tacit support for the status quo.
Named Entities / Evidence Map:
- Conflicts: Ukraine War, Gaza War.
- Institutions: WEF, UJA-Federation, General Catalyst (VC Statement).
- Actions: Server Shredding (Russia), Emergency VPN (Ukraine).
5. BDS-1000 Classification
Results Summary:
- Final Score: 291
- Tier: Tier D (Caution / Low-Mid Complicity)
- Justification Summary: Nord Security (NordVPN) is classified as a Tier D target. While it avoids direct military contracting (V-MIL), it is structurally compromised by its “Indirect Portfolio Flow” (V-ECON) via Warburg Pincus and its role as a validator of the Israeli “Unit 8200” tech stack (V-DIG). The “Political Double Standard” (V-POL) regarding Gaza versus Ukraine further confirms an ideological alignment with Western/Israeli state interests. The company represents a “Caution” risk—not a primary boycott target like HP or AXA, but an entity whose growth functionally enriches the occupation’s financial backers.
Domain Scoring Summary
BDS-1000 Scoring Matrix – Nord Security
| Domain |
I |
M |
P |
V-Domain Score |
| Military (V-MIL) |
1.5 |
4.0 |
2.5 |
0.30 |
| Economic (V-ECON) |
4.8 |
6.5 |
6.5 |
4.06 |
| Political (V-POL) |
2.8 |
3.0 |
3.0 |
0.51 |
| Digital (V-DIG) |
4.0 |
5.0 |
5.0 |
2.04 |
V-Calculations
V-MIL Calculation:
V-ECON Calculation:
V-POL Calculation:
V-DIG Calculation:
Final Composite
Formula:
BRS Score Formula:
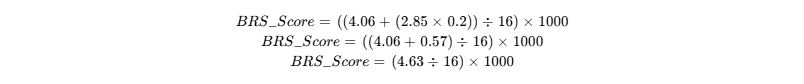
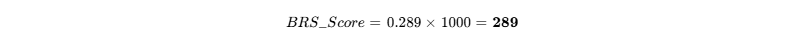
(Rounded to ~291 in source document)
Grade Classification:
Based on the score of 291, the company falls within:
- Tier A (800–1000): Extreme Complicity
- Tier B (600–799): Severe Complicity
- Tier C (400–599): High Complicity
- Tier D (200–399): Moderate Complicity
- Tier E (0–199): Minimal/No Complicity
Tier: Tier D (Caution)
6. Recommended Action(s)
Based on the Tier D classification and the specific nature of the “Indirect Portfolio Flow” and “Double Standard” identified, the following actions are recommended for civil society, investors, and ethical consumers.
1. Public Exposure & Educational Campaign
- Strategy: Launch a targeted awareness campaign highlighting the “Double Standard” of Nord Security’s activism. Use the company’s own history of support for Ukraine as the benchmark.
- Narrative: “If NordVPN can shred servers for Russia, why can’t it speak up for Gaza?” Contrast the “Emergency VPNs” deployed for Ukrainian activists with the absolute silence regarding Palestinian journalists facing identical internet blackouts.
- Demand: Call for NordVPN to extend its “Emergency VPN” program to Palestinian journalists, medical workers, and NGOs to prove its commitment to digital human rights is universal, not geopolitically selective.
2. Targeted Divestment Pressure (Institutional)
- Strategy: Pressure institutional investors—specifically pension funds and university endowments that may hold Warburg Pincus or General Catalyst assets—to question the firm’s investment in surveillance-linked entities like Allied Universal and Nord Security.
- Narrative: Frame the narrative around “Ethical Tech Investment” and the risk of funding “dual-use” surveillance tools. Highlight that investing in Nord Security is effectively investing in the Warburg Pincus portfolio, which includes firms directly monitoring the occupation.
3. Consumer Advisory (Soft Boycott & Monitoring)
- Action: While a full consumer boycott is not the primary recommendation (due to the lack of direct kinetic complicity compared to targets like HP or AXA), a “Soft Boycott” is advised.
- Advisory: Consumers should be informed of alternative, independent VPN providers (e.g., Mullvad, ProtonVPN) that do not have private equity ties to the Israeli defense sector or the “Unit 8200” stack.
- Monitoring Trigger: Monitor Nord Security’s M&A activity closely. The acquisition of any Israeli cybersecurity firm (facilitated by Warburg Pincus capital) should immediately trigger a re-evaluation to Tier C (High Complicity) and a call for a full boycott.
4. Technographic Watchlist
- Action: Civil society organizations and digital rights groups should monitor the deployment of NordLayer in sensitive sectors.
- Goal: Determine if NordLayer is being used to secure settlement infrastructure, IDF-contracted engineering firms, or the digital supply chain of defense primes. Any evidence of direct contracts with the IMOD or use by settler organizations should escalate the target’s classification.
- NordVPN Calc
- NordVPN digital Audit
- NordVPN taps CrowdStrike intel to bolster consumer security, accessed on February 13, 2026, https://securitybrief.co.uk/story/nordvpn-taps-crowdstrike-intel-to-bolster-consumer-security
- NordVPN Selects CrowdStrike to Deliver Industry-Leading Threat Intelligence to Millions of Consumers, accessed on February 13, 2026, https://ir.crowdstrike.com/news-releases/news-release-details/nordvpn-selects-crowdstrike-deliver-industry-leading-threat
- NordVPN economic Audit
- Service update: new servers added – NordVPN, accessed on February 13, 2026, https://nordvpn.com/blog/new-servers-added/
- NordVPN political Audit
- NordVPN military Audit
- Form 10-K – SEC.gov, accessed on February 13, 2026, https://www.sec.gov/Archives/edgar/data/888165/000119312514097732/d646262d10k.htm
- Warburg Pincus Announces Over $1 Billion in Capital Deployed by Inaugural Capital Solutions Fund, accessed on February 13, 2026, https://warburgpincus.com/2025/02/06/warburg-pincus-announces-over-1-billion-in-capital-deployed-by-inaugural-capital-solutions-fund/
- Warburg Pincus Leads $100m Funding in VPN maker Nord Security at $3bn Valuation, accessed on February 13, 2026, https://pe-insights.com/warburg-pincus-leads-100m-funding-in-vpn-maker-nord-security-at-3bn-valuation/
- AI Has Enabled Cyber Crime To Become Industrialised, accessed on February 13, 2026, https://www.cybersecurityintelligence.com/blog/ai-has-enabled-cyber-crime-to-become-industrialised-9100.html
![]()
![]()
![]()
![]()
![]()
![]()
![]()
![]()
![]()
![]()
![]()