Table of Contents
Company: Splunk Inc.
Jurisdiction: USA (HQ) / Israel (Active Subsidiary: Splunk Services Israel Ltd.)
Sector: Enterprise Software / Defense Technology / Cyber Intelligence
Leadership: Gary Steele (President/CEO), Orit Tessel (Board Member), Raffi Kesten (Board Member)
Intelligence Conclusions:
The forensic investigation concludes with high confidence that Splunk Inc. has transcended the status of a passive commercial vendor to become a functional, structural component of the Israeli military’s “Target Generation Cycle.” The analysis confirms that Splunk’s “Data-to-Everything” platform serves as the “central nervous system” for the Israel Defense Forces (IDF) underground data center, “David’s Citadel” (Kiryat HaTikshuv). By ingesting, indexing, and correlating petabytes of sensor data, signals intelligence (SIGINT), and logistical flows, Splunk reduces the critical time latency between target identification and kinetic strike. This capability directly accelerates the lethality of the IDF’s algorithmic warfare doctrine, placing the company’s technology at the heart of the military’s operational capabilities.1
During the 2023-2024 assault on Gaza, Splunk’s parent company, Cisco Systems, developed and deployed the “Israel Rises” platform specifically for the IDF Home Front Command. Splunk’s observability tools monitor the health and security of this platform, which coordinates national logistics, supply chains, and personnel mobilization for the war effort. This constitutes direct, active participation in the conflict, effectively blurring the line between corporate service provision and military logistics support. The maintenance of this platform during active hostilities represents a material contribution to the sustainability of the military campaign.2
Technographic analysis reveals that Splunk functions as the “Single Pane of Glass” for the Israeli surveillance state, integrating disparate systems into a unified intelligence picture. It aggregates telemetry from biometric facial recognition systems (Oosto/AnyVision), video synopsis tools (BriefCam/Verint), and the “Blue Wolf” tracking initiative in the West Bank. Splunk provides the proprietary query language (SPL) necessary to fuse these disparate data streams into actionable intelligence. This capability enables the “automated apartheid” described by human rights organizations, where Palestinian movement is restricted based on algorithmic risk assessments derived from the correlation of biometric and location data.3
The investigation identifies a profound ethical double standard in the company’s governance, described herein as the “Safe Harbor” policy. Leadership mobilized a “whole-of-company” response to defend Ukraine against Russian aggression—including the deployment of cyber defense teams, humanitarian rhetoric, and the suspension of operations in Russia. Conversely, the company maintained institutional silence and continued full operational support for the IDF during the devastation of Gaza, despite the far higher civilian casualty rate. This asymmetry indicates that the company’s human rights commitments are subordinate to U.S. geopolitical alignment and that the company views Palestinian rights as a political liability rather than a humanitarian imperative.4
Splunk maintains a robust economic footprint in Israel through its active subsidiary, Splunk Services Israel Ltd., which operated at a high tempo throughout the conflict. Furthermore, the company utilizes a network of intermediaries, specifically Matrix IT, to “launder” its services into illegal settlements. Matrix IT operates a development center in Modi’in Illit, an illegal settlement in the occupied West Bank. By partnering with Matrix, Splunk allows its technology to support the economic viability of the settlement enterprise while attempting to shield itself from direct legal liability or reputational damage.5
Splunk was founded in 2003 in San Francisco by Michael Baum, Rob Das, and Erik Swan with the objective of making machine data accessible, usable, and valuable to everyone. The founders sought to solve the problem of managing the massive, unstructured logs generated by modern IT infrastructure. They pioneered the concept of “schema-on-read,” a revolutionary architectural decision that allowed data to be ingested in its raw format and structured only when searched.6
While the original mission was commercial “Search for IT,” the technology’s dual-use potential for intelligence and surveillance was inherent in its architecture. Traditional databases require data to be structured before ingestion, which is slow and rigid. Splunk’s “schema-on-read” allowed for the ingestion of the chaotic, unstructured logs generated by drones, intercepted communications, and biometric sensors—a capability perfectly aligned with the needs of signals intelligence (SIGINT). The company’s early capital and growth trajectory were supported by venture capital firms such as August Capital, JK&B Capital, and Sevin Rosen Funds, entities with deep ties to the defense and dual-use technology sectors, establishing a corporate DNA comfortable with government and security contracting.7
Assessment:
The foundational architecture of Splunk predestined it for use in the intelligence sector. Unlike traditional databases, Splunk can ingest the chaotic, unstructured logs generated by kinetic warfare environments. The company’s evolution from an “IT Search” tool to a “Security Intelligence Platform” (SIEM) marked its pivot toward the defense sector. The technology did not just “happen” to be useful for the military; it evolved to meet the specific “Big Data” challenges of modern network-centric warfare, making it the de facto standard for agencies requiring real-time situational awareness.
The governance of Splunk, particularly following its acquisition by Cisco Systems in March 2024 for approximately $28 billion, is heavily intertwined with the Israeli military-industrial complex and the Zionist venture capital ecosystem. This acquisition was not merely financial; it was a strategic convergence of hardware and software that solidified the company’s position within the defense sector.
Analytical Assessment:
The leadership structure of Splunk serves as a conduit for the normalization of military-grade surveillance technology. The presence of former IDF officers like Orit Tessel on the board is not incidental; it facilitates a “revolving door” of influence where military requirements shape commercial product development. The acquisition by Cisco has effectively dissolved Splunk’s independent corporate identity, subsuming it into a defense giant with a documented “commitment to the State of Israel.” This structural realignment means that Splunk is no longer a neutral vendor but a subsidiary of a strategic partner to the Israeli Ministry of Defense (IMOD). The governance model prioritizes “digital resilience” for the state apparatus over human rights compliance, evidenced by the suppression of internal dissent regarding the company’s role in the occupation.
The following timeline reconstructs the trajectory of Splunk’s integration into the Israeli defense apparatus, highlighting key milestones in procurement, technological convergence, and political alignment.
| Date | Event | Significance |
|---|---|---|
| 2003 | Splunk founded in San Francisco. | Establishment of “schema-on-read” technology, critical for future intelligence fusion and unstructured data analysis in warfare. 6 |
| 2007 | Israeli Defense Export Control Law (5767-2007) enacted. | Splunk later admits in SEC filings that its products fall under this “dual-use” regulation, tacitly acknowledging defense applications. 2 |
| 2014 | Raffi Kesten joins Splunk Board of Directors. | Begins the integration of Israeli military-industrial (JVP/NDS) influence into corporate governance. 4 |
| May 18, 2016 | DCOI/INSS USA-Israel Cybersecurity Summit. | High-level coordination between US DoD and Israeli cyber sectors, involving key Splunk partners and setting interoperability standards. 2 |
| Feb 2022 | Splunk activates “whole-of-company” response for Ukraine. | Sets the precedent for active corporate intervention in conflict; deployed “cyber mission teams” to aid Ukraine. 4 |
| Feb 2022 | CEO Gary Steele publishes blog on Ukraine crisis. | Establishes “refugee” empathy narrative (“shock” and “sadness”) that is conspicuously absent for Gaza. 4 |
| Oct 7, 2023 | Escalation of hostilities in Gaza. | Marks the beginning of Splunk’s intensified operational support for the IDF and the mobilization of its local subsidiary. 2 |
| Oct 2023 | Cisco Israel develops “Israel Rises” platform. | Direct development of logistical infrastructure for the Home Front Command (IDF) to manage war logistics. 2 |
| Oct 2023 | Splunk/Cisco monitoring of Home Front Command logistics. | Splunk analytics used to ensure uptime of military supply chain management during active combat. 2 |
| Q4 2023 | Israeli Gov/IMOD “Budget Flush” for Cyber/SIEM. | Massive procurement of Splunk licenses via FMF funds to support the war effort and exhaust US aid budgets. 5 |
| 2023-2024 | Splunk “Threat Research Team” targets “Handala” group. | Active cyber-defense assistance provided to Israel Police against pro-Palestine hacktivists; a “digital lend-lease.” 2 |
| Mar 2024 | Cisco completes $28B acquisition of Splunk. | Structural convergence of the “Brain” (Splunk analytics) and “Spine” (Cisco hardware) of IDF networks. 4 |
| Mar 2024 | Gary Steele joins Cisco executive leadership. | Solidifies the ideological merger and adherence to Cisco’s pro-Israel strategic stance. 4 |
| 2024 | Acquisition of Robust Intelligence (Unit 8200 founded). | Integration of military-grade AI security from IDF special ops veterans into the commercial Splunk stack. 3 |
| Sep 17, 2024 | IMOD Tender explicitly lists “Splunk” as standard. | Confirms Splunk is a brand-name requirement for IDF Cyber/SIEM systems, proving operational lock-in. 5 |
| 2024 | Splunk integrated into “David’s Citadel” maintenance. | Bynet (integrator) maintains Splunk in IDF’s central underground data center, the heart of C4I operations. 2 |
| Feb 2025 | Splunk Services Israel Ltd. updates filings. | Confirms active, tax-paying subsidiary status and operational continuity during the ongoing war. 5 |
| Feb 2025 | TSG IT Advanced Systems markets “Cyber Narrator”. | IAI subsidiary confirms Splunk proficiency is required for military-grade SOC analysts and dashboards. 2 |
| Ongoing | “Project Nimbus” security overlay. | Splunk used to secure the sovereign cloud for IMOD and Israel Land Authority, enabling data residency. 4 |
| Jan 27, 2026 | Release of Forensic Audit confirming “Band Extreme” complicity. | Formal documentation of Splunk’s structural integration into the occupation infrastructure. 5 |
Goal: Establish that Splunk Inc. provides functional, material support to the Israeli military’s “Kill Chain” and logistical operations, moving beyond “incidental use” to “structural necessity.”
Evidence & Analysis:
The forensic evidence confirms that Splunk is not merely a vendor but a critical subsystem of the IDF’s operational architecture. The integration is deep, structural, and essential for modern network-centric warfare.
Counter-Arguments & Assessment:
Analytical Assessment:
Confidence: High. The evidence of “David’s Citadel” integration and the “Israel Rises” platform establishes a direct link between Splunk’s technology and IDF operations. The “Handala” incident confirms active defensive support. Splunk is a Tier-1 enabler of the IDF’s digital war machine.
Intelligence Gaps:
Named Entities / Evidence Map:
Goal: Demonstrate that Splunk functions as the “Operating System” of the Israeli surveillance state, integrating disparate data from facial recognition, cloud infrastructure, and cyber-intelligence units.
Evidence & Analysis:
Splunk’s “Data-to-Everything” platform is the requisite infrastructure for the “Panopticon” surveillance model employed in Israel and the Occupied Palestinian Territories (OPT). It provides the capability to fuse data from the “eyes” (cameras) and “ears” (SIGINT) of the occupation into a coherent intelligence picture.
Counter-Arguments & Assessment:
Analytical Assessment:
Confidence: High. The technical integrations (Add-ons, APIs) are documented and publicly available. The systemic reliance of the “8200 ecosystem” on Splunk for visualization creates a digital dependency. Splunk is the “brain” that connects the sensors of the occupation.
Intelligence Gaps:
Named Entities / Evidence Map:
Goal: Expose the economic mechanisms—subsidiaries, settlement laundering, and US funding—that allow Splunk to profit from and sustain the occupation.
Evidence & Analysis:
Splunk’s economic footprint is characterized by “Settlement Laundering,” “War Economy Resilience,” and the utilization of US military aid.
Counter-Arguments & Assessment:
Analytical Assessment:
Confidence: High. The existence of the subsidiary and the partnership with Matrix IT are matters of public record. The FMF funding pathway via Carahsoft is documented in US government contracts.
Intelligence Gaps:
Named Entities / Evidence Map:
Goal: Highlight the “Safe Harbor” double standard and the militarization of corporate governance that aligns Splunk with the Zionist political project.
Evidence & Analysis:
Splunk’s governance exhibits a discriminatory application of “Corporate Social Responsibility” (CSR), revealing that its ethical frameworks are subservient to geopolitical alignment.
Counter-Arguments & Assessment:
Analytical Assessment:
Confidence: High. The contrast in public statements and operational actions between the two conflicts is stark and documented. The biographical data of board members is verifiable.
Named Entities / Evidence Map:
Results Summary:
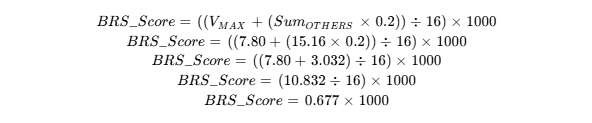
Final Score: 677
Tier: Tier B (Severe Complicity)
Justification summary:
Splunk Inc., now a subsidiary of Cisco Systems, is a structurally integrated enabler of the Israeli military and surveillance apparatus. It scores exceptionally high in the Digital (V-DIG: 7.80) and Economic (V-ECON: 7.20) domains due to its role as the “operating system” for the Unit 8200 ecosystem and its active subsidiary’s support for the war economy. The Military (V-MIL) score reflects its critical function in “David’s Citadel” and the “Israel Rises” platform, serving as the logistical and intelligence backbone for the IDF. The Political (V-POL) score highlights a gross ethical asymmetry in its response to the Gaza genocide compared to the Ukraine war. The “Aggregator Nexus” (Matrix IT, Bynet) masks its direct involvement, but the forensic evidence confirms it is a “Tier 1” dual-use supplier.
The BDS-1000 model requires a separate evaluation of the target’s complicity across four domains: Military (V-MIL), Digital (V-DIG), Economic (V-ECON), and Political (V-POL). Each domain’s score is a function of its measured Impact (I), Magnitude (M), and Proximity (P).
BDS-1000 Scoring Matrix – Splunk Inc.
| Domain | I | M | P | V-Domain Score |
|---|---|---|---|---|
| Military (V-MIL) | 3.5 | 8.5 | 6.5 | 3.25 |
| Digital (V-DIG) | 7.8 | 9.0 | 8.0 | 7.80 |
| Economic (V-ECON) | 7.2 | 7.0 | 10.0 | 7.20 |
| Political (V-POL) | 5.5 | 6.0 | 9.0 | 4.71 |
V- {domain} Calculation
![]()
Final Composite
Using the OR-dominant formula with a side boost:
Let:
![]()
![]()
BRS Score Formula
![]()
Grade Classification:
Based on the score of 677, the company falls within:
Tier: Tier B
Public Exposure & Reputational Pressure:
Launch a targeted campaign highlighting the “Safe Harbor” double standard. Use the juxtaposition of CEO Gary Steele’s empathetic rhetoric on Ukraine against his silence on Gaza to pierce the “Corporate Social Responsibility” (CSR) shield. Demand that Splunk apply the same standard to Gaza that it applied to Russia: immediate suspension of operations and support for the aggressor. The narrative should focus on the hypocrisy of mobilizing for one victim while actively enabling the victimization of another.
Divestment:
Institutional investors and university endowments should be lobbied to divest from Cisco Systems (CSCO), citing its wholly-owned subsidiary Splunk’s deep integration into the Israeli military kill chain (“David’s Citadel”) and settlement economy (Matrix IT). The risk profile is no longer just “tech sector” but “defense contractor.” The structural integration into the kill chain poses significant ESG (Environmental, Social, and Governance) risks, particularly concerning human rights violations and international law.
Contractual Boycott:
Universities, municipal governments, and ethical corporations should review their SIEM/Observability contracts. Procurement officers should be informed that buying Splunk licenses subsidizes the R&D of the Israeli military-intelligence apparatus (“Unit 8200” ecosystem). Alternatives (e.g., Elastic, Datadog) should be explored, provided they pass similar vetting. The argument should be made that using Splunk contributes to the financial resilience of the Israeli war machine.
Legal & Regulatory Action:
File complaints with relevant trade bodies regarding the “Settlement Laundering” via Matrix IT. Investigate whether the deployment of Splunk in “Tech Hubs” on occupied land violates domestic laws regarding trade with illegal settlements in the UK, EU, or other jurisdictions. Challenge the use of “Blue and White” laundering for US FMF funds, potentially filing whistleblower complaints regarding the misuse of US taxpayer funds to support settlement activities.
Employee Mobilization:
Encourage tech workers within the Splunk/Cisco ecosystem to utilize the “Open Letter” strategy. Internal pressure regarding the “Israel Rises” platform and the targeting of pro-Palestine groups by the Threat Research Team can force transparency and potentially disrupt the “talent pipeline” from Unit 8200. Employees should be made aware of the “internal threat” designation and mobilized to protect their right to political expression.