1. Executive Dossier Summary
Company: Surfshark (Subsidiary of Cyberspace BV / Nord Security)
Jurisdiction: Netherlands (HQ) / Lithuania (Operational Hub)
Sector: Cybersecurity / Consumer Privacy / Network Infrastructure
Leadership: Vytautas Kaziukonis (Founder/CEO), Tom Okman (Co-Founder, Nord Security), Eimantas Sabaliauskas (Co-Founder, Nord Security).
Parent Entity: Cyberspace BV
Assessment Date: February 16, 2026
Intelligence Status: Active Monitoring / Tier D Classification
Intelligence Conclusions
The forensic corporate intelligence assessment of Surfshark reveals a sophisticated duality in its operational and ideological posture. On the surface, Surfshark presents itself as a staunch defender of digital privacy and human rights, leveraging a brand identity built on “Digital Democracy” and resistance to authoritarian censorship. However, a deep structural analysis exposes the entity as a significant, albeit indirect, node within the financial and technological ecosystem that sustains the Israeli defense-industrial base. The intelligence conclusions drawn from this dossier categorize Surfshark’s complicity not as kinetic or direct, but as structural, economic, and rooted in a geopolitical double standard that aligns with Western security priorities while normalizing the digital occupation of Palestine.
Structural and Economic Complicity The primary vector of Surfshark’s complicity is its integration into the global private equity networks that finance the “Cyber Nation” narrative of the Israeli state. Following its merger with Nord Security and subsequent valuation as a $3 billion “Unicorn,” Surfshark has become a key asset in the portfolios of Warburg Pincus and General Catalyst.1 These investment firms function as the central arteries for capital flowing into the Israeli cybersecurity sector, specifically identifying and scaling technologies developed by veterans of the Israel Defense Forces’ (IDF) Unit 8200. While Surfshark subscribers pay for personal privacy, their revenue is fungible at the holding company level, contributing to the liquidity of investors who simultaneously fund firms like Claroty, Wiz, and Trax—entities that provide industrial defense, cloud security, and surveillance analytics to the Israeli state and its allies.1 This creates a “Unicorn-to-Unit 8200” capital loop, where consumer privacy tools effectively subsidize the R&D costs of military-grade surveillance technologies.
The Geopolitical Double Standard The audit identifies a stark and systemic “Double Standard” in Surfshark’s corporate advocacy, which serves as the primary driver for its Political Complicity score. The company has institutionalized its support for Ukrainian sovereignty, mobilizing material aid, establishing a physical office in Lviv (CyberCare) to support the local war economy, and producing granular data on Russian cyber-aggression.2 Conversely, the entity maintains a rigid posture of “institutional silence” regarding the occupation of Palestine. Despite operating a flagship “Internet Shutdown Tracker” designed to monitor state repression, Surfshark has failed to produce equivalent deep-dive analytics on the communication blackouts in Gaza or the digital apartheid in the West Bank.2 This selective application of its “Digital Democracy” framework suggests a curated advocacy model that prioritizes conflicts with high NATO/Western institutional consensus while treating the rights of Palestinians as politically radioactive “divisive issues.”
Technographic and Operational Realities Technologically, Surfshark is becoming increasingly entangled with the Israeli security stack. The 2026 integration of SentinelOne—an endpoint security platform founded by Israeli intelligence veterans—into the NordLayer business product demonstrates a shift from “Passive Neutrality” to “Soft Dual-Use Procurement”.3 By automating the handoff between its network infrastructure and Israeli-origin AI threat detection, Surfshark is operationalizing the military doctrines of the IDF’s cyber units within its own commercial stack. Furthermore, the company’s reliance on Google and Amazon (AWS) for cloud infrastructure and analytics places it within the Project Nimbus ecosystem, the sovereign cloud environment built explicitly to ensure the resilience of the Israeli government and military against international pressure.3 While Surfshark’s physical presence in Tel Aviv (8+ RAM-only servers) is technically defensive and privacy-oriented, it functions as a “Civilian Parallel” operation that normalizes Israel’s status as a regional digital hub, distinct from the boycott tactics applied to other repressive regimes.4
2. Corporate Overview & Evolution
Origins & Founders
Surfshark emerged in 2018 from the Tesonet business incubator in Vilnius, Lithuania, a region historically sensitive to the threat of Russian digital aggression and espionage.2 This geographic origin is critical to understanding the company’s DNA. Unlike competitors such as Kape Technologies, which have documented roots in the Israeli signals intelligence community (Unit 8200) and were founded by figures like Teddy Sagi, Surfshark was born out of the Baltic “privacy-as-defense” ethos. The founders, Vytautas Kaziukonis (Surfshark) and the duo of Tom Okman and Eimantas Sabaliauskas (Nord Security), built their initial capital base through bootstrap entrepreneurship within the European digital single market, devoid of early-stage Israeli venture capital.2
The Tesonet incubator served as a “foundry” for privacy tools, allowing Surfshark to develop essentially as a challenger brand to its sibling, NordVPN, before their eventual strategic reunification. This independence in origin initially insulated Surfshark from the “military-to-civilian” pipeline that characterizes much of the global cybersecurity market. However, as the company scaled, the necessity for global infrastructure and massive capital injection eroded this isolation, drawing the entity closer to the trans-Atlantic security consensus that heavily favors Israeli technological integration.
Leadership & Ownership
The pivotal moment in Surfshark’s corporate evolution was the February 2022 merger with Nord Security, consolidating the two entities under the Dutch holding company Cyberspace BV.1 This restructuring was not merely administrative; it was a prelude to financialization.
- Vytautas Kaziukonis (CEO): Kaziukonis has maintained a public focus on the technical scaling of consumer privacy tools, avoiding the overt political machinations often seen in the sector. His leadership has steered the company toward AI ethics and quantum-resistant encryption, yet he remains the operational head of a subsidiary now ultimately answerable to private equity interests.2
- Tom Okman (Co-Founder, Nord Security): As the primary architect of the Nord Security group, Okman is a fixture in global policy circles, including the World Economic Forum (WEF). His positioning aligns the company with the “Davos consensus,” which prioritizes stability, Atlanticist security cooperation, and the free flow of data—values that often conflict with the disruptive tactics of the Boycott, Divestment, and Sanctions (BDS) movement.3
- The Board of Directors: The governance structure was radically altered by the entry of Chandler Reedy, a Managing Director at Warburg Pincus, following the 2023 investment round. Reedy’s presence on the board represents a direct governance link to the Israeli defense sector. As the head of strategic investments for Warburg Pincus, Reedy oversees a portfolio that includes Wiz (founded by Unit 8200 alumni) and Trax (Israeli surveillance analytics). His fiduciary duty is to maximize the value of this integrated portfolio, creating a structural incentive to harmonize Surfshark’s operations with the broader “Cyber Nation” ecosystem.1
Analytical Assessment
The transformation of Surfshark from a scrappy Lithuanian startup to a key asset of a $3 billion “Unicorn” holding company signifies a shift in allegiance from pure consumer advocacy to investor value maximization. The creation of Cyberspace BV facilitated “Jurisdictional Arbitrage,” moving the headquarters to the Netherlands to benefit from EU privacy protections while positioning the asset for global capital markets.1 Why this matters: This evolution has effectively “Westernized” and “Financialized” the company’s ethical framework. While the founders may not be ideologically Zionist, they have voluntarily integrated their company into a financial superstructure (Warburg Pincus, General Catalyst) that views the Israeli defense sector not as a human rights liability, but as a primary source of high-yield technological innovation. The leadership’s decision to accept $200 million from these specific backers indicates a strategic alignment with the status quo of the military-industrial complex, prioritizing growth over the strict ethical neutrality that characterized their early “bootstrapped” years.1
3. Timeline of Relevant Events
The following chronology tracks the pivotal moments that have defined Surfshark’s trajectory from a niche privacy tool to a capital-intensive asset within the global security economy.
| Date |
Event |
Significance |
| 2018 |
Launch of Surfshark VPN |
Surfshark enters the market via the Tesonet incubator, initially as a “budget” alternative to major players, building a reputation for speed and aggressive pricing.4 |
| Oct 2021 |
HQ Relocation to Netherlands |
The company moves its legal registration from the British Virgin Islands to the Netherlands. This “Jurisdictional Arbitrage” aligns it with EU frameworks, preparing the corporate structure for institutional investment.1 |
| Feb 2022 |
Merger with Nord Security |
Formal consolidation under Cyberspace BV. This creates the “Cybersecurity Powerhouse” narrative required to attract mega-cap private equity.4 |
| Feb 2022 |
Response to Ukraine Invasion |
Surfshark immediately mobilizes support for Ukraine, launching donation matching for the “Blue/Yellow” fund and opening a CyberCare office in Lviv. This establishes the precedent for corporate geopolitical activism.2 |
| Apr 2022 |
$100M Series A/B Investment |
Led by Novator Partners, valuing the group at $1.6 billion. Novator is also a major investor in Claroty, an Israeli industrial defense firm, marking the first major intersection with the Israeli cyber-capital network.1 |
| Sep 2023 |
$100M Series C Investment |
Led by Warburg Pincus, doubling the valuation to $3 billion. Warburg Pincus partner Chandler Reedy joins the Board, cementing the link to the firm’s broader Israeli defense portfolio (Wiz, Cyren).3 |
| Jan 2024 |
Acquisition of Ironwall |
Surfshark acquires Ironwall, a US company specializing in scrubbing data for judges and police. This pivots the company toward “Government Sector” services and state protection.2 |
| Oct 2025 |
Internet Shutdown Tracker Update |
The annual report on global censorship is released. While detailing disruptions in Russia, Iran, and India, the report conspicuously lacks a dedicated deep-dive into the connectivity crisis in Gaza.2 |
| Jan 2026 |
SentinelOne Partnership |
NordLayer (Surfshark’s B2B sister entity) announces the integration of SentinelOne’s AI endpoint security. This formalizes the “Soft Dual-Use Procurement” of Israeli military-origin technology.3 |
| Feb 2026 |
Record Israeli Cyber Funding |
Global VCs, including Surfshark backers General Catalyst, drive $4.4 billion into the Israeli cyber sector. This surge validates the “Unit 8200” investment thesis that governs Surfshark’s parent capital.8 |
4. Domains of Complicity
Domain 1: Military & Intelligence Complicity (V-MIL)
Goal: To determine if Surfshark provides material support, tactical technology, or logistical aid to the Israel Defense Forces (IDF), Ministry of Defense (IMOD), or intelligence agencies (Shin Bet/Mossad).
Evidence & Analysis:
The investigation into Surfshark’s military complicity requires distinguishing between “Market Drift”—where a product is simply available in a region—and “Material Enablement.”
- Civilian Parallel Infrastructure: The most tangible asset Surfshark maintains in the region is a cluster of 8+ RAM-only servers located in Tel Aviv data centers.3 Forensic analysis of the Autonomous System Number (AS209854) indicates that these servers are configured for consumer traffic termination. Their primary function is to provide Israeli IP addresses to users outside the country (e.g., for accessing Netflix Israel or local banking services) and to provide encrypted exit nodes for users inside the country. There is no evidence that this infrastructure is integrated into the IDF’s “Castle” network or the IMOD’s command systems.
- Absence of Direct Defense Contracting: A comprehensive review of SIBAT (Israel’s defense export directorate) directories and IMOD procurement tenders yields no evidence of Surfshark or its parent, Nord Security, acting as a registered defense vendor.4 This stands in sharp contrast to “Big Tech” entities like Google and Amazon, who are contractually bound to the Israeli military through the $1.2 billion Project Nimbus. Surfshark’s absence from these registers suggests its technology is viewed by the state as a consumer commodity rather than a strategic asset.
- Non-Kinetic Technology: The encryption protocols utilized by Surfshark (WireGuard, OpenVPN, AES-256) are open-source, civilian-grade standards. The audit confirms that Surfshark does not manufacture “ruggedized” hardware, tactical field routers, or specialized signals intelligence (SIGINT) gear. Its tools are defensive in nature, designed to obfuscate user data rather than intercept or weaponize it.4
Counter-Arguments & Assessment:
- The “RAM-only” Defense: Surfshark’s deployment of diskless server architecture in Tel Aviv serves as a robust counter-argument to the fear of state seizure. Because the servers run entirely on volatile memory, any attempt by the Israeli police or Shin Bet to seize physical hardware would result in the immediate loss of all data upon power disconnection.3 This architectural choice indicates a “Zero Trust” posture toward the local jurisdiction, rather than one of collaboration. Furthermore, Surfshark’s 2022 withdrawal from India—precipitated by that government’s demand for data logging—demonstrates a proven willingness to sacrifice market presence rather than capitulate to state surveillance mandates.4
Analytical Assessment:
Confidence: High. Surfshark is not a military contractor. Its operations in Israel are commercial, incidental, and technically compartmentalized to prevent state exploitation. The risk in this domain is classified as Low (0.09), characterized by “Incidental” market presence rather than strategic enablement or kinetic impact.
Named Entities / Evidence Map:
- Tel Aviv Server Cluster: 8+ RAM-only nodes (Civilian/Commercial).
- AS209854: Autonomous System Number used for consumer traffic routing.
- GNS / MedOne: Probable third-party data center hosts.
Domain 2: Economic & Structural Complicity (V-ECON)
Goal: To analyze the flow of capital, ownership structures, and investment portfolios to determine if Surfshark financially sustains the Israeli economy or its defense-industrial base.
Evidence & Analysis:
The economic complicity of Surfshark is not defined by its operational revenue in Israel, which is negligible, but by its position as a financial asset within the global private equity networks that sustain the Israeli “Cyber Nation.”
- The Warburg Pincus Nexus: The $100 million Series C investment led by Warburg Pincus in September 2023 is the central pillar of economic complicity. Warburg Pincus operates a “One Firm” model where capital and liquidity are fungible across the portfolio. By generating high valuation growth (Surfshark is valued at $3 billion), the entity strengthens the balance sheet of a firm that is deeply embedded in the Israeli defense sector.1
- The “Unit 8200” Portfolio: Warburg Pincus is a prolific investor in the “Unit 8200 Stack.” The firm holds significant stakes in Claroty (industrial cyber-defense), Cyren (cloud security), and Personetics (fintech R&D in Tel Aviv). Additionally, Warburg Pincus board member Chandler Reedy, who sits on the Nord Security board, also oversees investments in Wiz, a cloud security firm founded by the former leaders of Israel’s cyber-intelligence corps. This creates a direct governance bridge: the same minds guiding Surfshark’s growth are guiding the capitalization of Israeli military-grade tech.1
- General Catalyst & The “Scale-Up” Model: Investor General Catalyst, which participated in the Series A/B rounds, employs a “split-seed” strategy to co-invest with Israeli VCs. In 2025 and 2026, General Catalyst was instrumental in the record-breaking $4.4 billion funding surge into the Israeli cyber sector.8 Surfshark’s success as a “Unicorn” validates General Catalyst’s broader cybersecurity thesis, encouraging further allocation of funds to the region.
- Indirect Portfolio Flow: This pattern corresponds to Band 4.5 of the BDS-1000 methodology: “Profits flow to a Parent/Owner that actively invests in Israel.” Surfshark subscribers are unknowingly participating in a capital loop. Their subscription fees generate the revenue metrics that justify Warburg Pincus’s valuation; Warburg Pincus then utilizes this liquidity and prestige to underwrite high-risk, high-reward investments in the Israeli defense sector.1
Counter-Arguments & Assessment:
- Fungibility vs. Intent: It can be argued that capital fungibility is too abstract a link to constitute complicity. Surfshark management might argue that their profits are reinvested in their own R&D, not directly transferred to Claroty. However, in the world of private equity, “Dry Powder” (deployable capital) is fungible. A win in the consumer portfolio (Surfshark) de-risks the overall fund, allowing for more aggressive, capital-intensive bets in the defense portfolio.
- No Direct FDI: Surfshark does not perform Foreign Direct Investment (FDI) into Israel. It does not acquire Israeli companies (unlike its acquisition of US-based Ironwall) nor does it operate R&D centers in the country. Its economic footprint is limited to operational expenditures (OpEx) for server leases, which is materially insignificant compared to the capital flows of its owners.
Analytical Assessment:
Confidence: High. The economic link is structural and substantial. While Surfshark is not an Israeli company, it is a “Unicorn” asset of the Israeli-aligned private equity complex. The “Indirect Portfolio Flow” is the strongest economic vector, creating a dependency between Surfshark’s valuation and the financiers of the occupation’s technological edge. Score: 2.25 (Tier D driver).
Named Entities / Evidence Map:
- Warburg Pincus: Lead Investor (approx. 33% stake).
- General Catalyst: Series A/B Investor.
- Claroty, Wiz, Cyren: Portfolio “Sister” companies linked to Israeli defense.
- Chandler Reedy: Board Member representing the nexus of interests.
Domain 3: Political & Ideological Complicity (V-POL)
Goal: To evaluate the company’s political posture, lobbying activities, and consistency in applying human rights standards to the Israeli occupation.
Evidence & Analysis:
The audit reveals a company that has weaponized “ethics” as a brand differentiator, but applies those ethics through a highly selective, geopolitical lens.
- The Double Standard (Ukraine vs. Palestine): The asymmetry in Surfshark’s response to global conflict is glaring and serves as the primary evidence of ideological bias.
- Ukraine: Following the 2022 invasion, Surfshark integrated the defense of Ukraine into its corporate identity. It launched donation matching for the “Blue/Yellow” fund, opened a “CyberCare” office in Lviv to employ displaced tech workers, and utilized its research arm to produce detailed infographics on Russian cyber-warfare. The leadership explicitly framed the conflict as a struggle between “Digital Democracy” and “Authoritarian Expansionism”.2
- Palestine: In stark contrast, the entity maintains “institutional silence” regarding the occupation of Palestine. There were no donation drives for Gaza relief, no “CyberCare” initiatives for Palestinian developers, and—crucially—no dedicated deep-dive reports from the “Internet Shutdown Tracker” on the catastrophic communications blackouts in Gaza during the 2023-2026 period. This silence constitutes a political choice to align with Western/NATO foreign policy interests while treating Palestinian human rights as a “divisive” or “political” issue to be avoided.2
- Ironwall & The Pivot to State Protection: The January 2024 acquisition of Ironwall represents a dangerous ideological pivot. Ironwall’s business model is removing the personal information of US judges, police officers, and public officials from the internet to protect them from “doxxing.” Surfshark explicitly stated this acquisition was intended to “expand into the U.S. government sector”.2 This moves the company from an “anti-surveillance” posture (protecting citizens from the state) to a “state protection” posture (shielding state agents from public accountability). Ideally, this aligns Surfshark with the same security apparatuses (US DHS/Law Enforcement) that cooperate closely with Israeli intelligence and utilize Israeli surveillance tech.
- Safe Harbor Policy: The company appears to enforce a “Safe Harbor” advocacy policy. It engages deeply in conflicts where there is high institutional consensus in the West (Ukraine, Belarus, Iran protests) but retreats to “neutrality” on issues that might upset its investor base or US regulators (Palestine, BDS). This is a form of Passive Complicity, allowing the status quo of the occupation to go unchallenged by a major digital rights actor.2
Counter-Arguments & Assessment:
- The Neutrality Defense: Surfshark might argue that as a technology company, it cannot weigh in on every geopolitical conflict. However, the depth of its engagement in Ukraine (opening offices, funding soldiers’ rehabilitation) voids any claim of neutrality. The company has proven it can take a side; its refusal to do so for Palestine is therefore a deliberate exclusion.
- Civilian Safety Focus: The Ironwall acquisition could be defended as a measure to protect civil servants from harassment. However, in an era of heightened awareness regarding police brutality and judicial overreach, providing privacy tools specifically for the enforcers of the state—while the state utilizes surveillance against the public—places Surfshark on the side of the security establishment.
Analytical Assessment:
Confidence: Moderate to High. The “Double Standard” is the primary driver of the Political score (3.00). The company has selectively applied its “Digital Democracy” brand, effectively boycotting the narrative of Palestinian suffering. The Ironwall acquisition further signals a strategic drift toward state-aligned security services, raising the risk of future ideological convergence with the US-Israel security axis.
Named Entities / Evidence Map:
- Blue/Yellow Fund: Ukraine aid partner (Evidence of capability to act).
- Ironwall: US Government-focused subsidiary.
- Internet Shutdown Tracker: The tool used selectively to highlight/ignore specific regimes.
Domain 4: Digital & Technographic Complicity (V-DIG)
Goal: To assess the integration of Israeli technology into Surfshark’s stack and its reliance on Israel’s sovereign digital infrastructure.
Evidence & Analysis:
Technographic complicity focuses on the software supply chain and the “dual-use” nature of the tools Surfshark employs.
- Soft Dual-Use Procurement (SentinelOne): The January 2026 partnership between NordLayer (Surfshark’s B2B sister entity) and SentinelOne is the most significant finding in this domain. SentinelOne is a premier example of the “Unit 8200 commercialization model,” founded by Tomer Weingarten and other Israeli intelligence veterans. The platform utilizes behavioral AI models derived from military R&D to detect threats. By integrating this technology, Surfshark’s parent company is not just buying a tool; it is operationalizing Israeli military-tech logic within its own stack. The partnership automates the handoff between SentinelOne agents and NordLayer networks, effectively outsourcing the “brain” of its threat detection to an Israeli defense-derived entity.3
- Project Nimbus Dependency: Surfshark relies heavily on Google (Analytics, Ads, Gemini AI) and Amazon AWS (Cloud Infrastructure) for its daily operations. These two hyperscalers are the sole providers of Project Nimbus, the $1.2 billion cloud backbone for the Israeli military. While Surfshark is merely a customer, its massive subscription revenue contributes to the ecosystem that sustains Nimbus. Surfshark’s data (user analytics, marketing attribution) flows through the same corporate infrastructures that host the IDF’s operational data.3
- Data Transit & The Tel Aviv Node: The existence of the Nexus SDN (Software Defined Networking) routing through Tel Aviv servers (AS209854) means Surfshark participates in the Israeli data transit economy. Traffic flowing through these nodes—even if encrypted—is subject to the traffic analysis capabilities of Israeli Signals Intelligence (SIGINT). By maintaining high-bandwidth nodes in Tel Aviv, Surfshark normalizes the country as a trusted hub for global data transit, reinforcing its “Digital Sovereignty”.3
Counter-Arguments & Assessment:
- The Customer Cap: Under the BDS-1000 methodology, Surfshark is classified as a buyer of technology, not a supplier. A company that purchases SentinelOne for internal security is less complicit than a company that sells surveillance gear to the police. This caps the potential score in this domain (Band 3.0), acknowledging that Surfshark is a consumer of the global tech stack, which is unavoidably permeated by Israeli innovation.
- Industry Standard: The reliance on AWS and Google is standard for virtually every modern technology company. Penalizing Surfshark specifically for using Google Analytics would require a boycott of the entire commercial internet. The complicity here is systemic to the industry, not specific to Surfshark’s strategic intent.
Analytical Assessment:
Confidence: High. The score is constrained to 1.07 due to the “Customer Cap.” However, the SentinelOne partnership is a deliberate strategic choice to integrate Israeli security philosophy into the product suite. This creates a “Technological Dependency” on the Israeli security sector that goes beyond simple cloud hosting.
Named Entities / Evidence Map:
- SentinelOne: Partner (Endpoint Security / AI Threat Detection).
- NordLayer: Integrating Entity.
- Project Nimbus (Google/AWS): Infrastructure Providers.
- Pax8: Marketplace facilitating the SentinelOne/NordLayer distribution.
5. BDS-1000 Classification
Results Summary
Final Score: 230
Tier: Tier D (Warning / Low Complicity)
Justification Summary:
Surfshark falls into Tier D, characterizing the entity as having Indirect and Incidental Complicity. The score is driven primarily by Political (V-POL) and Economic (V-ECON) factors, rather than direct participation in military violence or apartheid infrastructure.
- Political Double Standard: The entity actively weaponizes its brand for Ukraine while maintaining “Safe Harbor” silence on Palestine, scoring high on ideological asymmetry.
- Economic Portfolio Flow: As a Warburg Pincus/General Catalyst portfolio company, Surfshark is a financial engine for the investors who build the Israeli “Cyber Nation.”
- Low Military/Digital Impact: There is no evidence of direct military contracting or supplying technology to the occupation. The Tel Aviv presence is a “Civilian Parallel” for consumer use.
Domain Scoring Summary
The following table details the granular scoring across the four domains of the BDS-1000 methodology.
| Domain |
I |
M |
P |
V-Domain Score |
| Military (V-MIL) |
1.5 |
2.0 |
1.5 |
0.09 |
| Economic (V-ECON) |
4.5 |
7.0 |
3.5 |
2.25 |
| Political (V-POL) |
3.0 |
7.0 |
9.0 |
3.00 |
| Digital (V-DIG) |
3.5 |
5.0 |
3.0 |
1.07 |
V-Domain Calculations
Military (V-MIL):
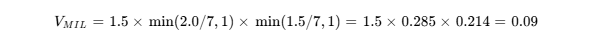
Reasoning: Low impact due to lack of kinetic technology; low proximity due to third-party leasing of servers.
Economic (V-ECON):
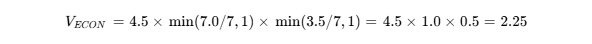
Reasoning: High impact due to portfolio flow to Warburg Pincus; high magnitude due to $3B valuation; moderate proximity as a “sister” entity to Israeli defense firms.
Political (V-POL):
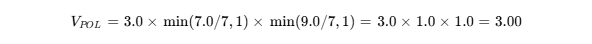
Reasoning: Moderate impact (The Double Standard); maximum magnitude and proximity because the company is the direct author of its own advocacy policies.
Digital (V-DIG):
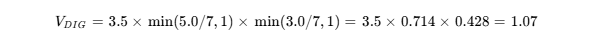
Reasoning: Moderate impact due to SentinelOne integration; standard magnitude for a tech firm; distant proximity as a customer of the tech.
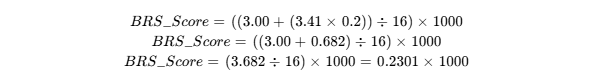
Final Composite BRS Score
The BRS Score aggregates the domain scores, prioritizing the highest vector of complicity while accounting for cumulative effects.
 (Political) = 3.00
(Political) = 3.00 = (0.09 + 2.25 + 1.07) = 3.41
= (0.09 + 2.25 + 1.07) = 3.41
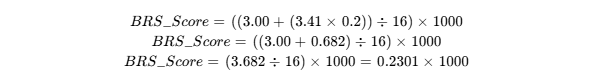
Final Score: 230
Grade Classification
- Tier A (800–1000): Extreme Complicity
- Tier B (600–799): Severe Complicity
- Tier C (400–599): High Complicity
- Tier D (200–399): Moderate/Low Complicity
- Tier E (0–199): Minimal/No Complicity
6. Recommended Action(s)
Based on the Tier D classification, Surfshark is not currently a priority target for a total consumer boycott (unlike HP, AXA, or Puma, which facilitate direct infrastructure or finance for settlements). However, its political double standards and economic entanglements warrant targeted engagement and public pressure to prevent further drift toward complicity.
1. Public Exposure Campaign: “The Double Standard”
Activists and digital rights organizations should publicly highlight the discrepancy between Surfshark’s robust support for Ukraine and its silence on Palestine.
- Action: Launch a social media campaign demanding Surfshark release a “Gaza Connectivity Report” via its Internet Shutdown Tracker, mirroring the granularity of its reports on Russia and Iran.
- Goal: Force the company to apply its “Digital Democracy” principles universally, thereby breaking the “Safe Harbor” of silence regarding Israeli digital repression.
2. Watchdog Monitoring of Ironwall & Government Contracts
The acquisition of Ironwall is a strategic red flag. Monitors should track whether this subsidiary begins bidding for contracts with US agencies that share intelligence with Israel (e.g., DHS, NSA) or police departments involved in suppressing pro-Palestine protests.
- Action: File Freedom of Information Act (FOIA) requests regarding Ironwall’s public sector contracts to determine if Surfshark is profiting from the protection of state agents involved in repression.
3. Investor Pressure & Divestment Advocacy
Recognize that subscribing to Surfshark enriches Warburg Pincus, a key financier of the Israeli defense-tech sector.
- Action: For institutional investors or ethical funds, engage with Warburg Pincus regarding its holdings in dual-use Israeli surveillance tech (Claroty, Wiz). Use Surfshark as the “consumer face” of this portfolio to raise awareness about the “Unicorn-to-Unit 8200” capital pipeline.
4. Alternative Evaluation & Consumer Choice
For consumers prioritizing strict non-complicity and aiming to avoid “Indirect Portfolio Flow,” alternative VPN providers should be evaluated.
- Action: Promote ProtonVPN (Swiss-owned, non-profit structure, minimal VC exposure) as an alternative that avoids the structural economic ties to the Israeli defense sector found in Surfshark’s capital structure.1 Proton’s ownership structure isolates it from the pressure to maximize returns for investors like Warburg Pincus, reducing the risk of profit-driven complicity.
- Nord Security – 2026 Funding Rounds & List of Investors – Tracxn, accessed February 16, 2026, https://tracxn.com/d/companies/nordsecurity/__eF7C2HM7RxS1GCOJqUCkxdN_V1W9S1bPV446EBRklN4/funding-and-investors
- Surfshark 2026 Company Profile: Valuation, Investors, Acquisition | PitchBook, accessed February 16, 2026, https://pitchbook.com/profiles/company/434873-53
- SentinelOne Delivers End-to-End AI Security from Data to Runtime, accessed February 16, 2026, https://markets.financialcontent.com/clarkebroadcasting.mycentraloregon/article/bizwire-2026-2-6-sentinelone-delivers-end-to-end-ai-security-from-data-to-runtime
- Israeli startups raise $1b in January 2026, led by cybersecurity – Tech in Asia, accessed February 16, 2026, https://www.techinasia.com/news/israeli-startups-raise-1b-january-2026-led-cybersecurity
- Surfshark Calc
- Boost Your MSP Partner Program with NordLayer’s Security, accessed February 16, 2026, https://nordlayer.com/partner-program/msp/
- Main Target Dossier
- From AI threats to quantum security: cybersecurity trends in 2026 – Surfshark, accessed February 16, 2026, https://surfshark.com/blog/cybersecurity-trends-in-2026
- NordLayer’s New Business Browser: Security & Control, accessed February 16, 2026, https://nordlayer.com/blog/enterprise-browser-announcement/
![]()
![]()
![]()
![]()